Crypto scams can feel devastating, but you’re not powerless. This guide explains how to report Bitcoin and cryptocurrency scams, who to contact, and how Digital Forensics experts can help trace funds and strengthen your case.

Report Cryptocurrency Scams – 24/7 Helpline:
(800) 849-6515
Every day, technology brings a new innovation to our doorstep. But at the same time, it opens the door to new, sophisticated scams. The same tools that benefit us also become detrimental when in the wrong hands. One such innovation is cryptocurrency. If you are reading this because you lost funds to a cryptocurrency scam, understand that you are not alone.
Cryptocurrency scams have skyrocketed over the past few years, mainly due to the anonymity they offer. The technology is relatively new, and not everyone has the digital literacy to understand how it works. On top of facing the unknowns, the lack of traditional bank oversight also plays a role in the mile-high surge in cryptocurrency scams.
Crypto scams can feel devastating, but you’re not powerless. If you are a victim of a crypto scam, the most critical step in having a chance at recovery is reporting the crime as soon as possible. Starting the reporting process early can prevent further loss and help in documenting the fraud with the finest details.
Understanding the Rise of Bitcoin and Cryptocurrency Scams
The reason behind the rise of Bitcoin and cryptocurrency scams is the level of digital literacy, coupled with a lack of laws and infrastructure that monitor digital currency transactions. Unlike traditional banking, where a fraudulent wire transfer might be reversed if caught quickly, the blockchain is immutable.
This means that if you confirm a transaction, even under the influence of false hope and psychological entrapment, it cannot be undone by a central authority. Bitcoin scammers play into this loophole, leveraging the power and global reach of the internet to target victims across borders.
The reason for this uptick isn’t only due to uncertainty and lack of knowledge around Bitcoin and cryptocurrency. Bitcoin scams often run in syndicates. These fraudulent groups also use psychological tactics, such as fear of missing out, natural inclination toward financial gain, and a need for emotional connection, to set up their cons.
By the time a victim realizes the “broker” is a bot, the funds have already been moved through multiple chains to obscure their origin. Reporting these incidents immediately is not just about your own recovery. It’s about providing the data points necessary to dismantle these global networks.
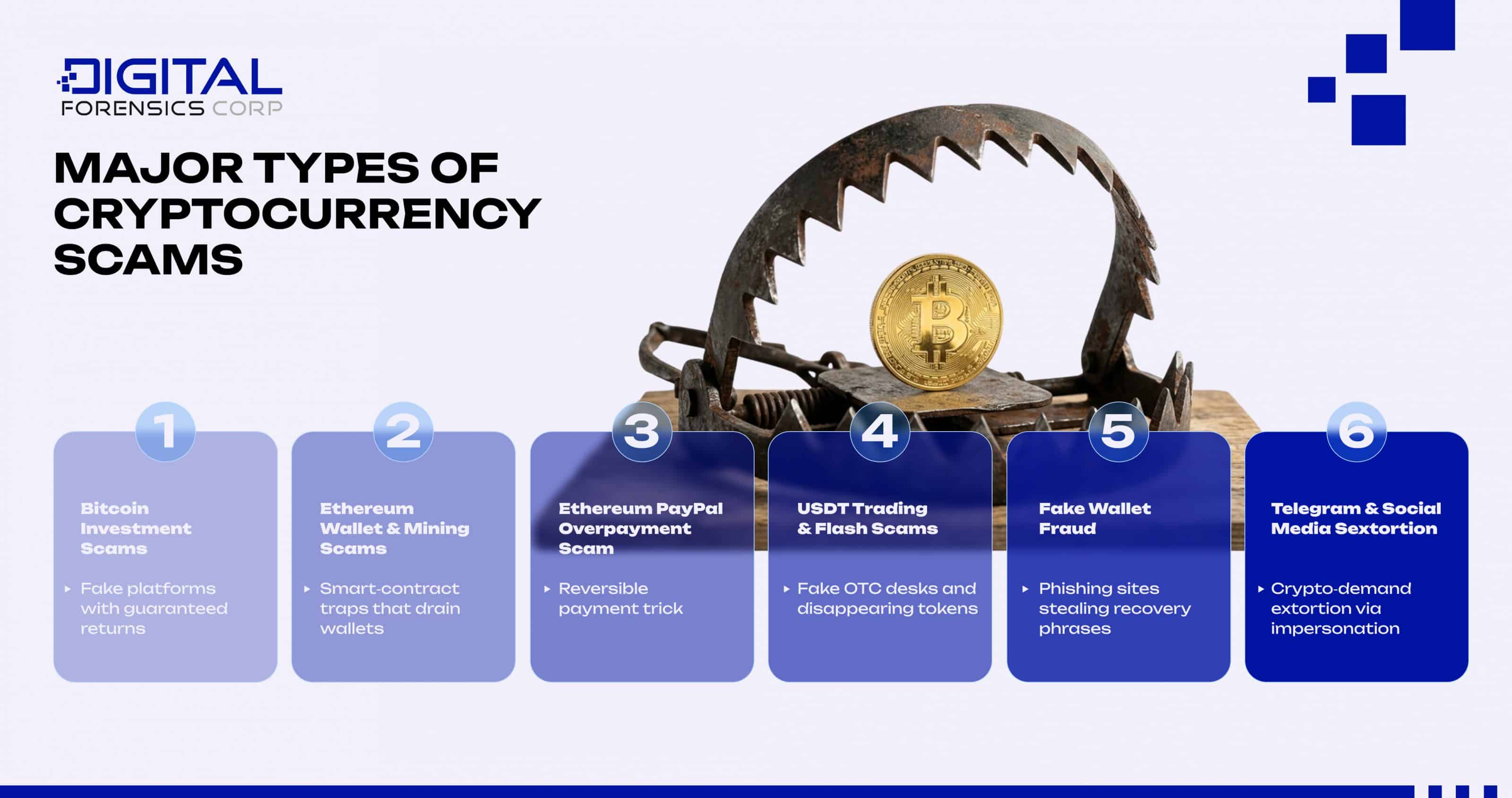
Common Types of Crypto Scams
Cryptocurrency scams are not straightforward. They are layered into different types, targeting and tailored to specific platforms and currency types. Understanding these types and their differences is essential in deciding how to report the cryptocurrency scam.
It helps categorize the crime for law enforcement and improves the accuracy of a Bitcoin scam investigation. The following are some of the most common types of cryptocurrency scams:
Bitcoin Investment Scams
This type of scam often utilizes a fake crypto platform, offering guaranteed returns. They sometimes present AI-generated false celebrity endorsements to lure in targets. Perpetrators use fake dashboards showing real-time returns, creating a false sense of trust.
However, when you attempt to withdraw your supposed profits, the “platform” demands IRS taxes, withdrawal fees, or anti-money laundering deposits.
Ethereum Wallet and Mining Scams
An Ethereum wallet scam occurs when the perpetrators gain unrestricted access to your crypto wallet. The victims are often invited to a liquidity pool offering “daily rewards”. It can also be simply a new “platform” to hold your assets.
Once you connect your crypto wallet to this new platform, you unintentionally sign a smart contract, buried in layers of the registration process, that grants the platform full access to your funds. The scammers get full access and the right to move your funds however they please.
Another common Ethereum-related scam is the Ethereum PayPal scam, where a buyer “overpays” you via a very reversible PayPal transaction. They then encourage you to send back the overpayment via Ethereum, which is non-reversible. Once you make this payment, they reverse their overpayment via PayPal.
USDT Trading and Flash Scams
Tether (USDT) is a favorite among scammers because of its price stability and perceived legitimacy. USDT trading scams often involve fake over-the-counter (OTC) desks or flash USDT. Flash USDT is a type of smart contract token that appears in your wallet but can very easily and legally vanish shortly after.
These USDT mining scams rely on the victim’s trust in stablecoins, lowering their guard and making them feel safer than they would with a volatile asset.
Fake Wallet Fraud
This works on the framework of phishing. The scammers create high-quality replicas of popular wallet software or platforms. They might send you a security alert email prompting you to enter your 12 or 24-word recovery phrase on a fake verification site.
Although an active digital user may be able to spot the differences on replicated platforms, a person with less digital knowledge can easily fall into this trap. Once they have access to the recovery phrase, they can recreate your wallet on their own device and sweep the funds in seconds.
Telegram and Social Media Sextortion
Another growing threat in cryptocurrency scams is Bitcoin sextortion abuse. Scammers may gain access to compromising video footage of you and demand payment in BTC to keep it private.
They often include an old password of yours sourced from a previous data breach as “proof” that they have hacked your profile. These can be empty threats or very legitimate sextortion attempts, and the psychological pressure makes them highly effective.
Targeted by a Crypto Scam? What You Should Do Immediately
If you fell victim to a crypto scam, you might be feeling scared, confused, and overwhelmed. But you must keep your head clear. The first 60 minutes after the attack is a golden hour for preserving evidence, securing your remaining assets, and having a strong chance at recovery. These 60 minutes decide how strong your Bitcoin fraud report will be.
Freeze & Secure: Your First 60 Minutes
First and foremost, cut all contact with the scammer. Continued communication only lets them know that you are reachable. If you must respond, employ delay tactics to buy time. You can say the transaction is processing or that you need time to set up and verify your account.
After stopping communication, change your passwords immediately. Enable 2FA using an authentication app. If you have shared any recovery credentials with the scammer, try to change them as soon as possible.
Additionally, if you have your credit card information linked to your crypto wallet, call your financial institution to alert them and report the scam activity. This can be beneficial in case they can flag the transaction as fraudulent before it clears.
The Evidence Checklist: What to Gather Before You Report
Before reporting cryptocurrency scam details to the authorities, you need a solid paper trail and digital footprint. Blockchain evidence is digital and must be logically organized. For this, we encourage you to complete the following item checklist:
- Capture Transaction Hash (TXID) for all the transactions made so far with the scammer. This is the “receipt” of the blockchain. It is a long string of letters and numbers.
- Look for and write down the scammer’s wallet address. This is synonymous with a bank account number. You can find it as the receiver’s address if you look at your transaction history in the past 60–120 minutes.
- Save every chat on Telegram, WhatsApp, or whichever platform you communicated with the perpetrators. Do not delete the conversation; export it if the app allows. If it doesn’t, take as many screenshots as you can. Copy and store any links they might have sent you.
- If you were a victim of a fake wallet scam, take a screenshot of the original email alert. Try to capture screenshots of the fake wallet or platform before the scammer takes it down. Write down all the emails and contact info you see in the email thread.
- Store the original links to the fake investment or mining sites. Also, take screenshots of the platform if it is still up.
- When recording evidence, list all dates and timestamps for every activity and communication. Also, note down the specific amounts sent in both crypto and USD value for each separate transaction and in total.
How to Report Bitcoin and Cryptocurrency Scams (Step-by-Step Guide)
In Bitcoin scams, reporting is not just an option. It is the foundation of funds recovery and protection. You should submit your case to multiple law enforcement agencies to ensure maximum visibility across different jurisdictions.
- FBI Internet Crime Complaint Center (IC3): The IC3 is the primary US agency for digital fraud. When you report crypto scams, FBI agents use the data to identify large-scale patterns and criminal syndicates. Be as detailed as possible in the “description” box.
- Federal Trade Commission (FTC): Report the fraud with the FTC. The FTC tracks consumer trends and helps build civil cases against fraudulent platforms and deceptive marketing.
- Securities and Exchange Commission (SEC): If the scam involved a token investment, initial coin offering (ICO), or a fake exchange, you should inform the SEC. They have a specific online form for Tips, Complaints, and Referrals (TCR).
- Local Cybercrime Units: While small-town police may not be equipped to handle crypto-related crimes, larger city departments often have dedicated cybercrime divisions that can file an official police report.
- The Crypto Exchange: If you have sent money from a centralized exchange like Coinbase, Binance, or Kraken, notify their fraud department immediately. They can blacklist the destination address and provide information if the scammer has an account there.
Reporting Crypto Scams by Coin Type or Platform
The strategy for a crypto scam investigation can change depending on the technology involved. For example, tracing a Bitcoin transaction is different from tracing an Ethereum-based token like USDT. We will break down these differences in the sections below.
Bitcoin Scams
Bitcoin uses a UTXO model, which means every transaction leaves change behind. Investigators can trace these change outputs to see where the coins sit or if they are being sent to a mixer. Because Bitcoin is the most liquid crypto, it is often the first “hop” in a scammer’s chain.
Ethereum and USDT Scams
Ethereum scams often involve smart contracts. For Ethereum wallet scams, investigators must look at the contract’s code to see where the withdrawal function is sending assets. USDT scams are unique because USDT is a centralized stablecoin. The company Tether has, in specific legal circumstances, frozen stolen USDT if provided with a court order or a law enforcement request. This makes reporting USDT fraud particularly time sensitive.
Platform-Specific Fraud
If the scam happened via a Reddit Moons trade, a Telegram signal group, or a PayPal-to-Crypto exchange, the platform itself becomes a witness. You must report the user profiles to these platforms to prevent them from claiming more victims while the blockchain investigation proceeds.
What to Do After You Report a Crypto Scam
Once the reports are filed, your focus shifts to long-term digital hygiene and monitoring. Victims are often targeted a second time because their information is sold on “sucker lists” to other scammers.
Monitoring and Hardening
Monitor your credit report through services like Experian or TransUnion to ensure the scammers did not steal your identity along with your crypto. If you gave the scammer access to your computer via software like AnyDesk or TeamViewer, you must assume the entire machine is compromised. Wipe the device and reinstall your operating system.
Preserving the Chain of Custody
Keep all your communication evidence in a secure, backed-up folder. Do not edit or crop screenshots. Law enforcement needs the original files to verify their authenticity. If you see the stolen funds moving to a known exchange via a blockchain explorer like Blockstream or Etherscan, update your IC3 report with the new transaction hashes. This real-time data is often what triggers an active investigation.
Prevention: How to Avoid Bitcoin and Crypto Scams
The most effective way to handle cryptocurrency scams is to build a “firewall” around your behavior. Most scams rely on social engineering rather than technical hacking.
- Verify everything. If a “financial advisor” reaches out on LinkedIn or Instagram, assume they are a scammer. Real advisors do not solicit clients via DM for crypto investments.
- Use reputable platforms. Make sure to use only legitimate platforms that include security and consumer protection features. Only access these exchanges through their official websites, not links that are shared with you.
- Use hardware wallets. Keep your long-term holdings on a device like a Ledger or Trezor. This prevents “drainer” scripts from taking everything if you accidentally click a bad link.
- Check the URL. Scammers create perfect clones of sites like Binance or Uniswap. Bookmark the real sites and never click links from emails or “sponsored” Google search results.
- The “Too Good to Be True” rule. If an offer promises 1% daily returns, that would equal over 3,650% annually if compounded. No legitimate business on earth offers this. High-yield USDT mining scams are almost always Ponzi schemes.
How Digital Forensics Experts Help Trace and Report Crypto Scams
While law enforcement is often spread thin, digital forensics crypto experts provide the dedicated resources needed for a deep dive into the blockchain. We utilize professional-grade analytics tools that go far beyond what is available to the public.
Our investigators specialize in following the money through complex layers, including mixers, tumblers, and cross-chain swaps. We provide comprehensive Bitcoin scam help by creating a certified forensic report. This report maps out exactly where your funds went and identifies the “off-ramps”—the points where the scammer converts crypto back into fiat currency at an exchange.
By presenting law enforcement with a pre-packaged investigative file, you significantly increase the chances of your case being prioritized. We collaborate with legal teams and exchanges to ensure that when stolen funds hit an account tied to a real identity, the proper authorities are notified. If you are feeling overwhelmed by the technical jargon of a Bitcoin fraud report, our team acts as your navigator through the process.
The aftermath of a scam is a race against time. If you have been targeted and need to report cybercrime or document the fraud for law enforcement, contact Digital Forensics Corp. for expert guidance. Our team provides the cryptocurrency scam help and technical precision required to navigate the complexities of blockchain investigation. Whether you need a formal Bitcoin scam investigation or help tracing Ethereum assets across various protocols, we are here to strengthen your case and support your path to justice.
FAQs
These scams involve inviting victims to join a fake “liquidity pool” or mining group that supposedly generates passive income. The victim is asked to “connect” their wallet to a DeFi site, which is actually a malicious smart contract that gives the scammer the power to drain the wallet’s contents at any time.
You should report these to the FBI’s IC3 and the FTC immediately. Additionally, you should notify the wallet provider (like MetaMask or Trust Wallet) and the centralized exchange where you originally purchased the assets. If the scam involves USDT, contacting the issuer, Tether, with a police report can sometimes be an additional step.
Yes, using advanced blockchain forensic tools, our investigators can trace the path of stolen assets across multiple wallets and blockchains. While we cannot manually reverse a transaction, we provide the evidentiary reports that law enforcement and exchanges require to take action and potentially freeze assets.
Look for red flags like “no hardware required” mining, guaranteed daily payouts, or the requirement to “invite friends” to increase your hash rate. Legitimate mining requires massive computational power and does not happen through a simple browser-based “liquidity node.”
Investigators will map the flow of funds to identify a “choke point,” such as a centralized exchange where the scammer has a KYC-verified account. Once an exchange is identified, law enforcement can issue a subpoena or a freeze order to prevent the scammer from withdrawing the money.
Recovery is a complex process that depends on the scammer making a mistake, such as moving funds to an exchange that follows strict banking laws. While not guaranteed, having a professional forensic report drastically improves the likelihood of a successful recovery through legal channels.
This is a form of digital blackmail where a scammer claims to have hacked your webcam and recorded you during private moments. They demand a “silence fee” in Bitcoin. These are almost always scams based on leaked email/password databases, and no such video actually exists.
Watch for “investment gurus” who DM you with no‑risk pitches, pressure to act fast, refuse to video chat, or demand crypto payments labeled as “taxes” to unlock profits. While real investing carries risk, high pressure, secrecy, or requests for private keys are clear red flags of scams.
You can sue, but it’s extremely difficult. Scammers are often anonymous or overseas, and tracing wallets is hard. You can sue identifiable perpetrators or negligent platforms. It’s also possible to file John Doe suits. However, your best immediate step is to report the fraud to the FBI/IC3 and preserve evidence.
A crypto scammer is a criminal who uses the hype around digital currency to steal money. They use fake apps, “guaranteed” deals, or romance to convince you to send crypto. Because transactions are decentralized and permanent, funds can vanish instantly and are hard to recover.






