When data matters, how it’s collected matters even more. Digital Forensics Corp. provides expert forensic data acquisition services designed to preserve evidence accurately, securely, and defensibly.
Expert Digital Forensic Data Acquisition Services for Investigations
Digital forensic investigations begin with one critical step: collecting evidence correctly. Data acquisition in digital forensics ensures that electronic data is copied, preserved, and verified without altering the original source. Whether the case involves fraud, cybercrime, internal corporate disputes, or online blackmail, the process must follow strict forensic standards, so the evidence can withstand legal scrutiny. Improper collection methods can compromise entire investigations. That is why organizations and individuals rely on expert data acquisition services to gather digital evidence safely and maintain its integrity throughout the investigation lifecycle.
What Is Digital Forensic Data Acquisition?
Digital forensic data acquisition is the process of collecting and preserving electronic evidence from devices such as computers, mobile phones, servers, and storage drives. The objective is to create a bit-for-bit copy of the original media without modifying the source data.
Unlike routine IT backups or file transfers, forensic data acquisition preserves every piece of information exactly as it exists, including hidden files, deleted artifacts, and system metadata. This approach allows investigators to analyze evidence without altering the original device.
During the acquisition process, forensic specialists use write-blocking technology to prevent any modifications to the evidence. Once the copy is created, investigators conduct their analysis on the duplicate rather than the original device. This ensures the source media remains intact and can be verified later if necessary.
Why Forensic Data Acquisition Is the Foundation of Every Investigation
Every digital investigation depends on trustworthy evidence. If digital evidence is collected improperly, the entire case can be compromised. A digital forensic investigator doesn’t replace police involvement. Instead, they complement the efforts of law enforcement by carefully extracting evidence and ensuring it is properly preserved.
Improper handling may result in:
- Altered timestamps.
- Missing or corrupted data.
- Evidence being ruled inadmissible in court.
- Legal challenges related to the chain of custody.
Organizations rely on forensic data acquisition in many situations, including:
- Cybercrime and fraud investigations.
- Internal corporate investigations.
- Intellectual property disputes.
- Employee misconduct cases.
- Online blackmail and sextortion investigations.
It’s essential to know how to properly document evidence of an online scam. Preserving digital evidence presents unique challenges compared to preserving traditional evidence. This data typically resides on digital media or in the cloud. In both cases, recovering evidence in its original form can be a daunting task. Before documenting the evidence, you should understand the steps of the process.
How Forensic Data Acquisition Works
Imaging vs. Live Acquisition
Forensic imaging creates a mirror copy of a storage device. This copy contains every sector of the drive, including deleted data and system files. Imaging is commonly used when investigators can safely power down a device.
Live acquisition occurs when the system must remain running. This method captures volatile information such as system memory, active network connections, or running processes.
Preserving Chain of Custody
Chain of custody refers to the documented handling of evidence from collection through analysis. Every transfer, access point, and storage location is recorded.
Ensuring Forensic Soundness
Forensic soundness means the acquisition process preserves data exactly as it existed. During imaging, forensic software generates verification hashes such as MD5 or SHA-1.
These cryptographic hashes act as digital fingerprints. If the hash of the copied evidence matches the original source, investigators can prove the data remained unchanged.
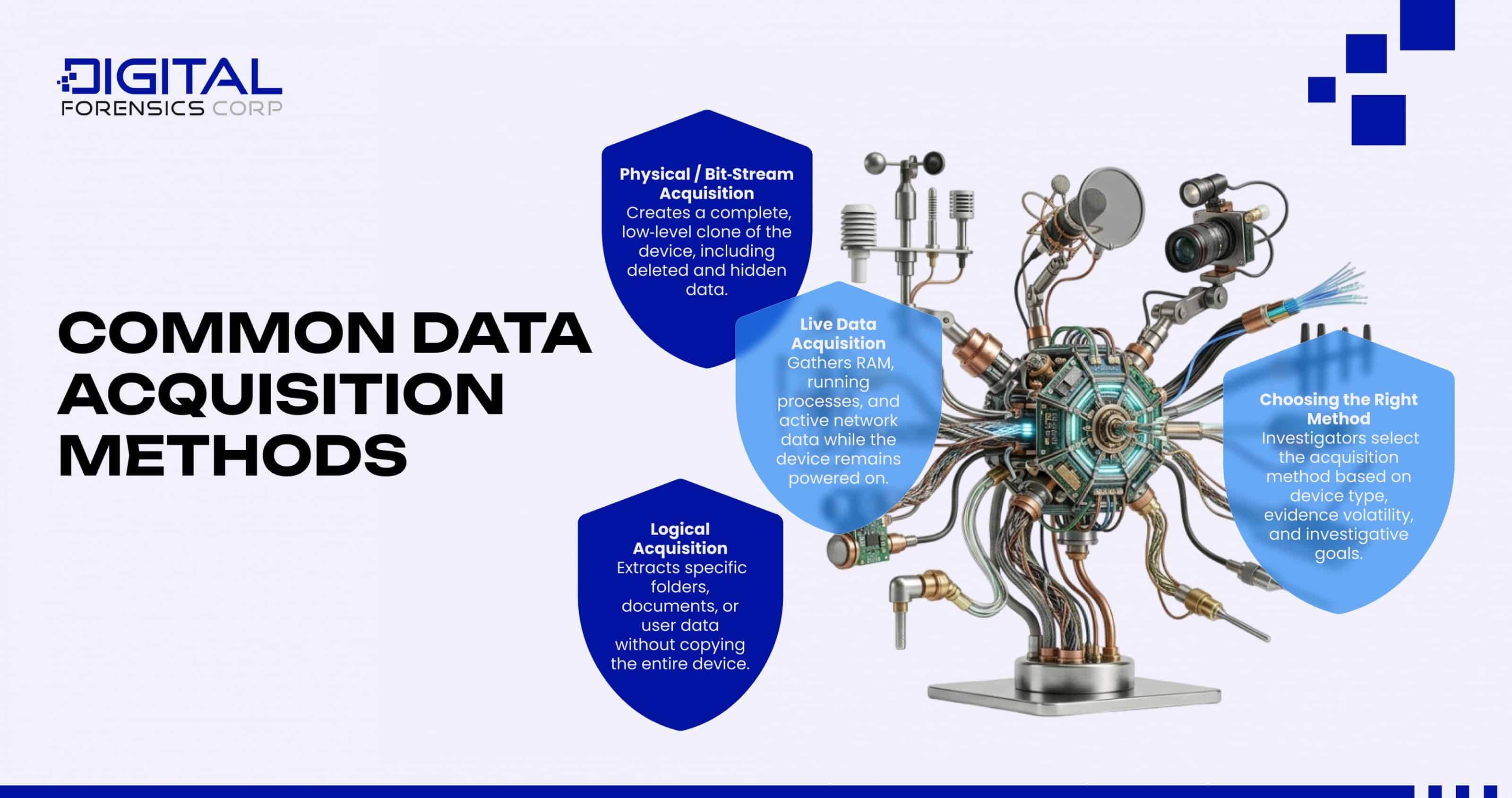
Common Data Acquisition Methods in Digital Forensics
Digital forensic investigators rely on several data acquisition methods depending on the device and investigation requirements.
- Logical acquisition captures selected files or directories from a device.
- Physical or bit-stream acquisition copies every sector of the storage media.
- Live data acquisition collects volatile system information while the device remains active.
Each technique serves a different investigative purpose. Selecting the correct method is a key responsibility of expert data acquisition professionals.
On-Site vs Remote Forensic Data Acquisition Services
Data acquisition services can be performed either on-site or remotely, depending on the circumstances of the investigation. On-site forensic data acquisition is typically required when devices cannot leave their location. This often occurs during corporate investigations, legal holds, or situations involving complex or sensitive equipment.
On the other hand, secure remote collection allows investigators to preserve data quickly while minimizing operational disruption. It is often faster and cheaper than on-site recovery because travel logistics are eliminated. However, it requires efficient communication and can be less effective with highly intricate investigations.
Challenges and Risks in Digital Forensic Data Acquisition
Encryption and Locked Devices
Modern devices often use strong encryption. While encryption improves security, it can complicate digital forensic data acquisition if investigators cannot access the protected data.
Volatile Data and Live Systems
Certain data exists only while a device is powered on. Memory artifacts, system processes, and network connections disappear once the device shuts down.
Anti-Forensic Techniques
Cybercriminals sometimes deploy anti-forensic tools to hide or destroy evidence. These techniques may include data wiping, log manipulation, or encryption.
Maintaining Chain of Custody and Forensic Integrity
Chain of custody is one of the most critical aspects of any digital investigation.
Every step of evidence handling must be carefully documented. Investigators record device identifiers, acquisition timestamps, system configurations, and verification hashes. By following strict forensic procedures, expert data acquisition teams prevent data alteration and maintain the authenticity of the collected evidence.
Digital Forensics Corp.’s Expert Approach to Data Acquisition
Digital Forensics Corp. provides expert data acquisition services for organizations, legal professionals, and individuals involved in digital investigations. Our forensic engineers are trained to collect and preserve digital evidence. Using industry-standard forensic tools and verified acquisition procedures, we ensure that evidence is preserved accurately and securely.
By combining technical expertise with strict forensic protocols, we help clients gather defensible evidence that can withstand legal and investigative scrutiny. Our acquisitions strictly adhere to data collection protocols to provide proof that no information has been deleted or tampered with during the acquisition process.
When DIY Data Collection Can Damage Your Case
Many individuals attempt to collect evidence themselves by copying files or screenshots. While these actions may seem helpful, they can unintentionally damage critical evidence. Opening files, moving data, or powering devices on and off can modify timestamps or overwrite important artifacts. For this reason, organizations and individuals are strongly encouraged to rely on trained professionals when digital evidence must be preserved.
Start a Forensic Data Acquisition with Digital Forensics Corp
Digital evidence can disappear quickly. Files may be deleted, systems overwritten, or devices replaced. At DFC, our team consists of certified digital investigators, data analysts, and legal counsel who are well-versed in cyber law. We hold offices around the world with an established network of affiliates on every continent.
Through proprietary tools and techniques, we can help you retrieve and preserve evidence, assess threats and risks, and analyze digital footprints with the goal of identifying the perpetrators responsible. We collaborate with law enforcement around the globe to help our clients bring criminals to justice.
Outside of the initial threat, our team can strengthen your online security framework and implement practices to mitigate the chances of similar scams in the future. You can feel confident that our entire investigation will be documented, and the findings will only be discussed with authorized parties.
If you need to secure digital evidence for an investigation, contact Digital Forensics Corp. for expert data acquisition guidance. Our staff is available 24/7 to hear your case. Don’t hesitate. Contact us today to speak with one of our specialists and get started with a free consultation
FAQ
What is digital forensic data acquisition?
Digital forensic data acquisition is the process of collecting and preserving electronic evidence from digital devices without altering the original data. Investigators create verified copies of storage media so they can analyze the evidence while maintaining the integrity of the original source.
How is forensic data acquisition different from regular data copying?
Regular data copying transfers selected files, while forensic data acquisition creates a complete bit-for-bit image of the device. This method preserves hidden files, deleted artifacts, and system metadata, ensuring evidence remains legally defensible.
What data acquisition methods are used in digital forensics?
Common methods include logical acquisition, physical or bit-stream acquisition, and live data acquisition. Each technique is used depending on the device, investigation requirements, and whether the system must remain powered on.
Can individuals perform forensic data acquisition themselves?
While individuals may attempt to copy files, proper forensic data acquisition requires specialized tools and training. Incorrect handling can modify timestamps or damage evidence, which may affect investigations or legal proceedings.
When is live data acquisition required?
Live acquisition is necessary when investigators need to capture volatile data such as system memory, active processes, or network connections. This information disappears once the device is powered down.
What devices can forensic data acquisition be performed on?
Forensic data acquisition can be performed on computers, servers, mobile devices, storage drives, cloud systems, and removable media such as USB drives or memory cards.
Why do organizations need expert data acquisition services?
Organizations rely on expert data acquisition services to ensure digital evidence is preserved properly for legal, regulatory, or internal investigations. Professional handling helps maintain the chain of custody and protects the integrity of the evidence.
How long does digital forensic data acquisition take?
The timeline depends on the size of the storage media, the complexity of the system, and the type of acquisition performed. Smaller devices may take a few hours, while enterprise systems can require significantly more time.






