Cybercrimes are growing at a rapid pace, targeting businesses and governments worldwide. Automation and generative artificial intelligence (AI) have transformed cyberattacks, including extortion, sextortion, and malware, making them highly profitable for attackers.
According to Scott Schelble, Deputy Director of the Federal Bureau of Investigation (FBI), the FBI’s Internet Crime Complaint Center (IC3) received more than 80,000 complaints in 2025, with reported losses totaling $2.9 billion.
To combat these attacks, the FBI provides resources for reporting cybercriminals. This guide will walk you through what cybercrimes the FBI handles, how to collect and preserve electronic evidence, the steps to file a report to the IC3, and the state of cybercrimes in today’s digital world.
What Services Does the IC3 Provide for Cybercrime Victims?
The IC3 serves as a centralized platform for reporting internet-based crimes. While the center itself does not investigate individual complaints, it provides the following services:
- Complaint Submission: Victims can submit a detailed report of the crime through the IC3’s online complaint form. This information is shared with relevant law enforcement agencies for investigation.
- Data Analysis: The IC3 analyzes trends and patterns in cybercrime to support broader FBI investigations and public awareness campaigns.
- Resource Guidance: The IC3’s website provides resources for victims, including steps to mitigate the impact of the crime, such as freezing credit reports or strengthening cybersecurity measures.
- Collaboration with Other Agencies: The IC3 works with various agencies, including federal, state, and local law enforcement partners, to address cybercrime effectively.
Steps to File a Cybercrime Report with the FBI’s IC3
Emergency Complaint
In some circumstances, you may need immediate help. If so, dial 911 for quick help. You can also call your local police to deal with imminent danger.
Routine Complaint
To report cybercrime and online extortion to the IC3, follow these steps:
1. Visit the IC3 Website: Go to www.ic3.gov and select the option to file a complaint.

Figure 1: IC3 “File a Complaint” Page
Once you click the “File A Complaint” button, a new pop-up window appears asking you to either accept or decline the terms of service.
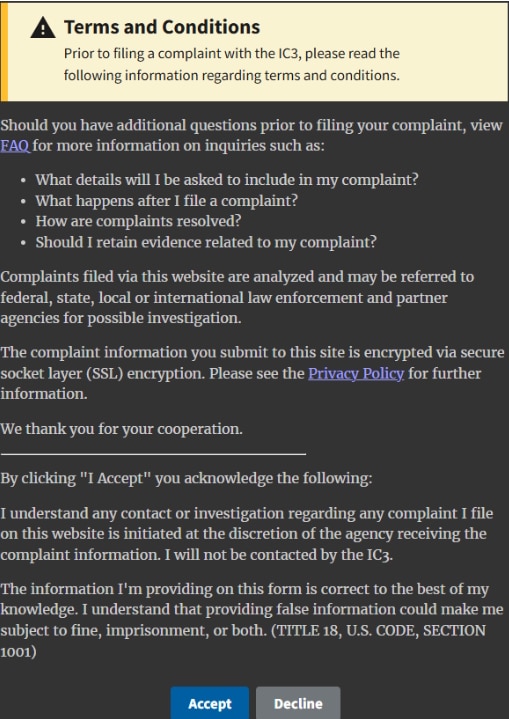
Figure 2: IC3 Terms and Conditions
2. Fill Out the Form: Once you accept the terms of service, you will be redirected to the IC3 complaint form page. The form will ask you to go through seven steps, which include:
- Who is Filing this Complaint?
- Complainant Information
- Financial Transaction(s)
- Information About the Subject(s)
- Description of Incident
- Other Information
- Privacy & Signature
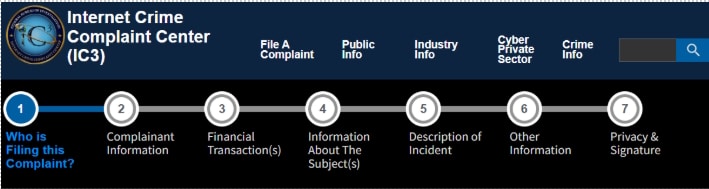
Figure 3: IC3 7-Step Process to File a Complaint
It is important to note that IC3 does not typically require the complainant to provide Personally Identifiable Information (PII), such as Social Security numbers.
3. Follow Up: While you may not receive individual updates, you can track trends and news through IC3’s public reports.

Figure 4: Digital Forensics Corp. Complaint Filing Guidance
What Happens After You File a Cybercrime Report with the FBI’s IC3
Once you have filed a complaint, an FBI-trained analyst will review and research your complaint. They will disseminate information to law enforcement and relevant partner agencies.
It’s important to note that the IC3 doesn’t directly investigate cybercrimes. Instead, the report is filed and forwarded to the appropriate agencies, who will investigate and prosecute the responsible parties when possible. After submitting the complaint, you will receive the following official message from the FBI.
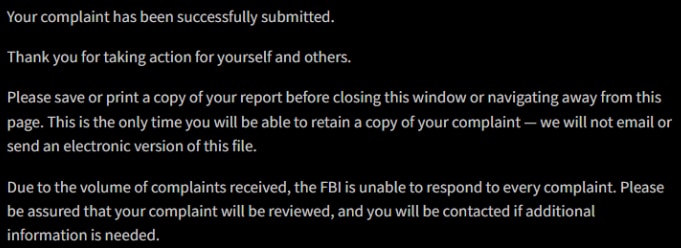
Figure 5: IC3 Official Message After Submitting a Complaint
The experts at Digital Forensics Corp. can assist you with follow-up plans, documentation, and communication with authorities. In this situation, you are not alone. Our company can assist your efforts to take back control and recover your data.
What Cybercrimes Does the IC3 Handle?
The FBI’s Internet Crime Complaint Center (IC3) is designed to process reports of cybercrimes affecting individuals and businesses in the United States. They deal with a wide range of cybercrimes, including:
- Phishing
Phishing is a fraudulent attempt to obtain sensitive information by masquerading as a trustworthy entity. Today’s scammers leverage AI to create highly convincing phishing campaigns.
They may request documents, credentials, or urgent payments. In other cases, malware-infested links are disguised as routine messages. Once access is gained, attackers leverage stolen information for extortion. - Identity Theft
Identity theft is the act of someone using another person’s PII to commit fraud or other crimes. Common forms of identity theft include:- Medical identity theft. Using someone else’s insurance to make false medical claims.
- Tax identity theft. Submitting fraudulent tax returns in someone else’s name to claim refunds.
- Financial identity theft. Gaining unauthorized access to financial data to compromise existing accounts or open new ones.
- Sextortion
According to the FBI, sextortion crimes involve threatening and coercing teens and children into sending explicit images and videos online. Sextortion can begin on any website, app, or game. That is why extortion reporting is essential.
Sextortionists can be ruthless, and their sextortion schemes are always changing as they adapt their tactics. AI technology has enabled sextortion attempts even in cases where no intimate content was shared. No matter their angle, their goal is to make you believe you have no option but to pay. - Ransomware
Ransomware remains one of the highest-loss categories reported to the IC3. It’s a malicious cryptography attack in which threat actors encrypt essential files on the victim’s device. They demand payment for decryption and threaten to permanently delete or publicly release the data if they aren’t met with compliance. - Business Email Compromise (BEC)
BEC scams are a form of fraud where threat actors impersonate trusted leaders to trick employees into disclosing corporate data or sending money. These attacks can result in millions of dollars in losses. Common types of BEC scams include attorney impersonation, account compromise, and CEO fraud. - Distributed Denial of Service Extortion
A distributed denial-of-service (DDoS) attack occurs when a malicious actor floods a server or network with traffic, preventing normal access. Some criminals use this pressure tactic to combine disruption with payment demands. They threaten prolonged downtime of the system or data if a ransom is not paid. - Data Breach Extortion
A data breach involves unauthorized access to confidential or protected information. Insider threats and external attacks are the primary causes. Insider threats are employees who may misuse their access to harm the company, while external parties carry out network attacks.
In breach-based extortion, criminals often threaten to release stolen customer data or misuse corporate secrets. They demand payment in exchange for not following through on their threats. - Social Engineering: The Art of Deception
Internet criminals aren’t always easy to identify. Sometimes they use sophisticated tactics to impersonate others or gain your trust. This is otherwise known as social engineering. Instead of using highly technical skills to hack into a network, scammers use social engineering to trick users into letting them in.
Hackers can also take over an employee’s or trusted individual’s account to trick co-workers into sharing sensitive information. It’s important to keep your guard up in every interaction online. Be cautious of all links and take your time when reading or responding to messages.
When Should You Report to Another Agency?
While the IC3 handles a wide range of cybercrimes, certain situations may require you to report to a specialized agency. Below are examples of incidents and the agencies that handle them:
- Crimes Involving Children: If the crime involves child exploitation, such as the distribution of child pornography or online grooming, it should be reported to the National Center for Missing & Exploited Children (NCMEC) through their CyberTipline at www.missingkids.org.
- Financial Crimes: For scams involving investment fraud or other complex financial crimes, consider reporting to the Securities and Exchange Commission (SEC) or the Federal Trade Commission (FTC) in addition to the IC3.
- Local Matters: For crimes that appear to be localized, such as harassment or revenge porn from someone known to you or small-scale fraud, you might want to contact your local police department first. They can coordinate with the FBI if necessary.
- Health-Related Scams: If a cybercrime involves fraudulent medical services or the illegal sale of medications, report it to the U.S. Food and Drug Administration (FDA) or Medicare’s Fraud Hotline.
Next Steps for cybercrime Victims After Filing an IC3 Report
Reporting cybercriminals is a critical step in combating online threats and protecting yourself and others from future harm. The IC3 serves as a valuable resource for addressing a variety of internet-based crimes, but knowing when to report blackmail online to specialized agencies can ensure your complaint is directed to the appropriate authorities. If you’re facing threats and looking to file a Cybercrime report, the IC3 is often the best place to start.
If you are a victim of extortion or cybercrime, experts at Digital Forensics Corp. are available 24/7 to assist you. We provide many services to investigate the cybercrime using state-of-the-art technology. You can use our investigation to file a report with law enforcement, and we also have legal professionals that can provide support or direct you to an attorney that can help you seek justice. For immediate assistance with any cybercrime, contact Digital Forensic Corp. today!
Common Cybercrime Cases We Investigate
Digital Forensics Corp. deals with a broad spectrum of threat landscapes. If you have fallen prey to a cyberattack or a data breach, our highly skilled forensic investigators and cybersecurity professionals can help you get out of this nightmare.
Our team effectively deals with cyber extortion, including sextortion and image-based blackmail, BEC, ransomware, phishing, and identity theft. Our team uses advanced techniques, such as our proprietary IP-to-location technology, to gather evidence and provide an expert cybercrime report.
You can use our investigation to file a report with law enforcement, and we also have legal professionals who can provide support or direct you to an attorney who can help you seek justice. For immediate assistance with any cybercrime, contact Digital Forensics Corp. today.
FAQs
How do I report cybercrime to the FBI or IC3?
You can dial 911 in an emergency and file a complaint with the IC3. In the latter scenario, you will have to file a report through their online portal or contact your local field office.
What should I include in a cybercrime report?
The IC3 requires the complainant’s information, including name, address, telephone, and email address. You will also provide details of financial loss and transaction information.
What happens after I report cyber extortion to FBI?
The IC3 assigns your report to the receiving agency, which may further investigate the case and let you know its status.
Can Digital Forensics Corp. help after I file my report to FBI?
Yes, Digital Forensics Corp. can certainly help you with follow-up plans, documentation, and communication with authorities.