Losing access to the important data saved on your locked Android phone or tablet can feel scary. You may have lost access to your phone or device because of a broken screen, forgotten passcode, or a need to access the internal storage.
Luckily, your important data is still stored in your device and there’s a chance the important information has been backed up, stored on external storage, and the files can be accessed using a few methods.
For some, a factory reset is out of the question when trying to unlock a locked Android phone. Getting access to the device to use it again in its used state and factory reset are not the same thing.
A factory reset will make data recovery impossible, restoring the phone or tablet to the way you received it when you first bought the device. Data recovery can be successfully performed on a device without the need for a reset or formatting.
Instances where a phone or tablet screen is broken or a device is potentially in disrepair could still allow you to gain access. However, a cracked screen would likely need to be fixed before the Android device and its data can be retrieved by the user.
In this article, we’ll be covering some more advanced methods to unlock a locked Android smartphone or device.
Is It Possible To Recover Files on a Locked Android?
Traditionally, you would need to unlock your phone or tablet by entering your secure PIN or phone password to access it. Using a USB cable and treating the device like a plug-in device would be ineffective unless the phone or tablet has been set to do so.
A locked Android device that is inaccessible to the user by entering the PIN can still have its files recovered. The data you’re looking to access may be stored internally, externally, or tied to an accessible account that allows you to unlock the device without the PIN.
With more advanced methods where the PIN and account credentials are unavailable, the key is to enable USB debugging mode before the device needs to be accessed. Below, we will cover the methods professionals use to recover files that would otherwise be lost.
So, is it possible to unlock a locked Android smartphone? The answer is “yes” with a but, depending on whether the device is yours and what levels of access you have. If the first few methods don’t work or aren’t applicable, you’ll need some experience with computers, a USB cable compatible with your phone, and some light knowledge of SQL (databases).
If you’re fairly familiar with computers but not sure about SQL, we’ll only be touching on it briefly; however, a small introduction to it may help you perform the needed procedure.
Getting Started
Before we jump into making changes to the database of your phone it’s a good idea to ensure that the Android device is truly inaccessible. This means you’ve tried to unlock it through one of the following methods:
- Try any possible PINs you may have used in the past
- Use Samsung‘s SmartThings Find tool for Samsung phone or tablet devices
- See if the data you want to access is stored on an SD card as part of its external data storage.
If all those methods are unsuccessful or not applicable, we can move to the more advanced options. In this case, you’ll want to gather the needed program and items.
But first, let’s try a less advanced method:
Access Your Phone Through Your Google Account
When it comes to data backup, iPhones use iCloud, and Androids use Google. To prevent data loss, your first step in recovering data should be to use your Google account to unlock your device.
To use this feature, you would have to set up and sign up to sync and connect your phone to a Google account.
- Step 1: Find the “forgot password?” feature on your phone’s locked home screen.
- Step 2: Answer the recovery questions used to set up your Google account. If you’re not sure of the answers, move on to the next step.
- Step 3: Enter any password five times to trigger a “Forgotten the password” feature.
- Step 4: Enter your Google account credentials. With the correct credentials provided, you’ll have access to your device with no loss of data and no PIN entered.
ADB (Android Debug Bridge)
ADB is a command-line tool used to communicate with an Android device. It allows the user to directly interact with the phone or Android device.
With this method, you would be sending commands to your phone to modify files stored within the device and gain access. This method would require you to have access to a computer and a USB cable.
To use this method your phone will need the USB debugging mode to have been previously enabled. If this method isn’t activated beforehand and the phone is inaccessible to do so, you will not be able to send commands through ADB or access the bootloader.
Most devices are shipped with the debugging mode disabled and the bootloader locked. If you’re unsure if you’ll be able to access your phone through the ADB shell using a USB cable you can follow the steps below to see what methods are available to you.
How To Recover Data From a Locked Android
There are two main types of locks: Pattern and PIN/Password. To crack it, a forensic examiner needs to extract one or two files from the mobile device.
Of course, there is no universal solution, but there are three main options for recovering your Android’s data.
3 Options for Recovering Android Phone Data:
- To use Android Debug Bridge. The mobile device being examined must be rooted and USB debugging must be enabled.
- To flash a custom recovery. The device’s bootloader must be unlocked.
- To use JTAG or Chip-off techniques.
To crack Pattern lock, you need just one file located at /data/system/. The filename is gesture.key.
This file contains an unsalted SHA-1 hash of the device Pattern lock. The number of patterns is limited due to each number (0 – 8) can be used only once. To crack it, a rainbow table with all possible variations needs to be created.
We are not going to reinvent the wheel because talented digital forensics analysts from CCL have already created a Python 3 script that can solve the problem. You can download it here. Run the script, and in about 30 minutes, you’ll get an sqlite database with all possible pattern hash variants. Now, you can search the DB for hash extracted from your gesture.key file.
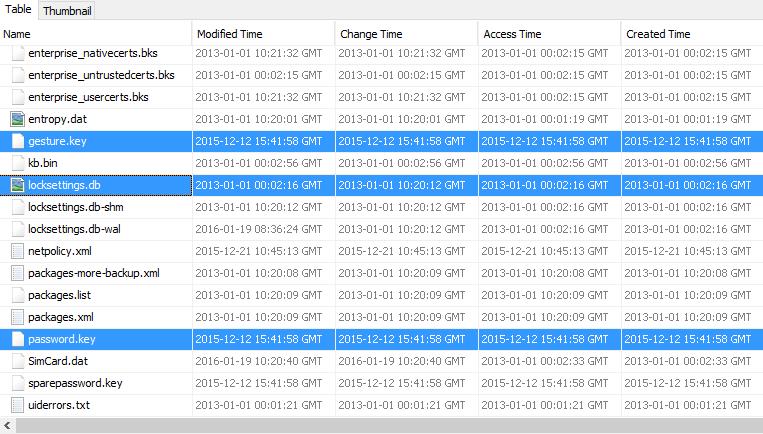
To crack the PIN or password, you need two files. The first file is password.key, located at /data/system/, the second – settings.db (for Android prior to 4.4), located at /data/data/com.android.providers.settings/databases/, or locksettings.db (for Android 4.4 and higher), located at /data/system/.
We need two files instead of one because, this time, the hash is salted. In settings.db, the salt can be found in the “secure” table in locksettings.db — in the “locksettings” table. Use your favorite SQL browser to find the lockscreen.password_salt key.
Of course, if you are a hex editor addict, you can use your favorite tool. Now it’s time to use oldy-moldy brute-force. And again, CCL has a Python 3 script to solve the problem. It can be downloaded here. To start cracking, you should run the script with the hash, the salt and max code length (4 – 16).
To tell the truth, you don’t even need to crack Pattern, PIN or password. You can bypass it by deleting the relevant files. Of course, it’s not forensically sound. Nevertheless, this is the only way to bypass Lollipop device locks.
Mobile Device Discovery
If you’re facing a situation where recovering data from your Android device is imperative but you’re not able to implement the steps laid out above, Digital Forensics Corp can help. If your locked Android phone or tablet contains the information you need, we are ready to help you retrieve that information using special data recovery software.
Digital Forensics Corp employs certified engineers to recover data through:
- Imaging
- Data recovery
- Data analysis
- Forensic analysis
- E-Discovery
If the smartphone device has specific data that needs to be accessed our team can help you dissect the information within. We can get as detailed as identifying which cell phone towers were used to handle a call, text, or send phone data through or simply recovering the data on a locked Android phone or tablet. Our phone forensics experts are ready to help.
Sources:
How does SmartThings Find (Find My Mobile) work? | Samsung






