The “Hello Pervert” email is a common sextortion scam. Learn how this email scheme works, how to identify sextortion threats, and what to do if you receive a blackmail email.
There are more forms of communication today than ever before. As the internet continues to evolve, cybercrime tactics evolve alongside it. Despite advancements in messaging platforms, email remains the most common entry point for cyberattacks, with a significant percentage of attacks beginning with phishing or malicious email campaigns.
Online users continue to report blackmail and sextortion emails as a widespread issue that affects thousands of individuals every year. These scams do not discriminate—anyone with an email address can become a target. Among these threats, one of the most recognized and widely reported formats is the “Hello Pervert” email scam.
This scheme is not sophisticated from a technical standpoint, but it is highly effective due to its psychological manipulation. Understanding how it works is the first step toward protecting yourself. Read on to learn more about the “Hello Pervert” scam.
What is the ‘Hello Pervert’ Email?
A “Hello Pervert” email is a mass-distributed sextortion scam template used by cybercriminals to threaten recipients into paying a ransom. These emails are sent to hundreds or even thousands of people at once using lists obtained from data breaches or public leaks.
The message typically claims that the sender hacked your device weeks ago and has gained full access to your files, browsing history, and webcam. It often alleges that you were recorded while viewing adult content and performing explicit acts.
The email then escalates into a threat. The sender claims they will distribute the alleged footage to your family, friends, or colleagues unless you pay a ransom—usually in cryptocurrency such as Bitcoin or Litecoin. The attacker may promise to delete the content after payment, but this is almost always false.
This tactic is known as webcam sextortion. It typically relies on fear, embarrassment, and the assumption that the victim will panic and comply without verifying the claims. In reality, webcam compromise does not truly occur in a vast majority of cases. However, legitimate hacking is possible, and all threats should be handled seriously.
The most common psychological triggers in “Hello Pervert” scams include fear of exposure, shame, urgency, and perceived authority. When a message claims your privacy has already been violated, it creates a sense of immediate crisis. Adding a countdown timer, such as 24 or 48 hours, forces rushed decisions.
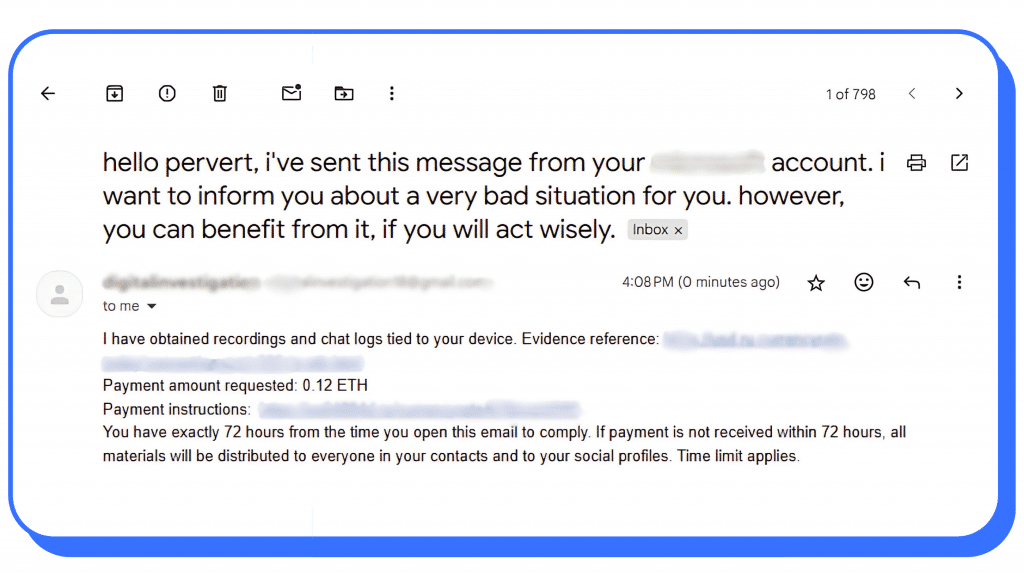
Real ‘Hello Pervert’ Extortion Email Example
| Subject: Hello Pervert you have been hacked |
|---|
I’ll be notified when you open my email, and from that moment you have exactly 48 hours to send me cryptocurrency to <wallet_address_placeholder>. If cryptocurrencies are unchartered waters for you, don’t worry, it’s very simple. Just google “crypto exchange” and then it will be no harder than buying some useless stuff on amazon. I strongly warn you against the following:
Also, don’t forget that cryptocurrencies are anonymous, so it’s impossible to identify me using the provided address <wallet_address_placeholder>. Good luck, my perverted friend. I hope this is the last time we hear from each other. |
These instructions in “you have been hacked” or “Hello Pervert” emails are not technical safeguards. They are psychological pressure tactics designed to isolate you and prevent rational decision-making.
What If the “Hello Pervert” Email Appears to be From Your Own Account
Cybercriminals do not rely on hacking in these scams. Instead, they rely on human behavior. Receiving a message with the subject line, “you have been hacked pervert,” puts pressure on the victim. The structure of a “Hello Pervert” email is carefully designed to trigger emotional responses that override logic.
It’s common for scammers to send sextortion emails to victims using their own email addresses. This is known as email spoofing, and cybercriminals use this tactic to convince recipients that their email accounts have been compromised. You might see your own email address in the ‘From’ section, but that is a forged address. Scammers can use software to put fake information in the header. However, email filters can detect and flag these emails as spam.
Variations of the “Hello Pervert” Email Scam and How They Work
While the “Hello Pervert” format is widely recognized, cybercriminals use several variations of email-based extortion. Understanding these differences helps you assess whether a threat is credible or fabricated.
Some emails are entirely fake and rely on generic scripts with no real evidence. Others may include malicious attachments designed to install malware. In other cases, attackers may possess real compromising content obtained through data breaches, hacked accounts, or prior scams.
Additionally, many attackers request payment through cryptocurrency because it is difficult to trace and cannot be reversed. Others use spoofed email addresses to make the message appear as though it was sent from your own account, increasing the perceived credibility of the threat.
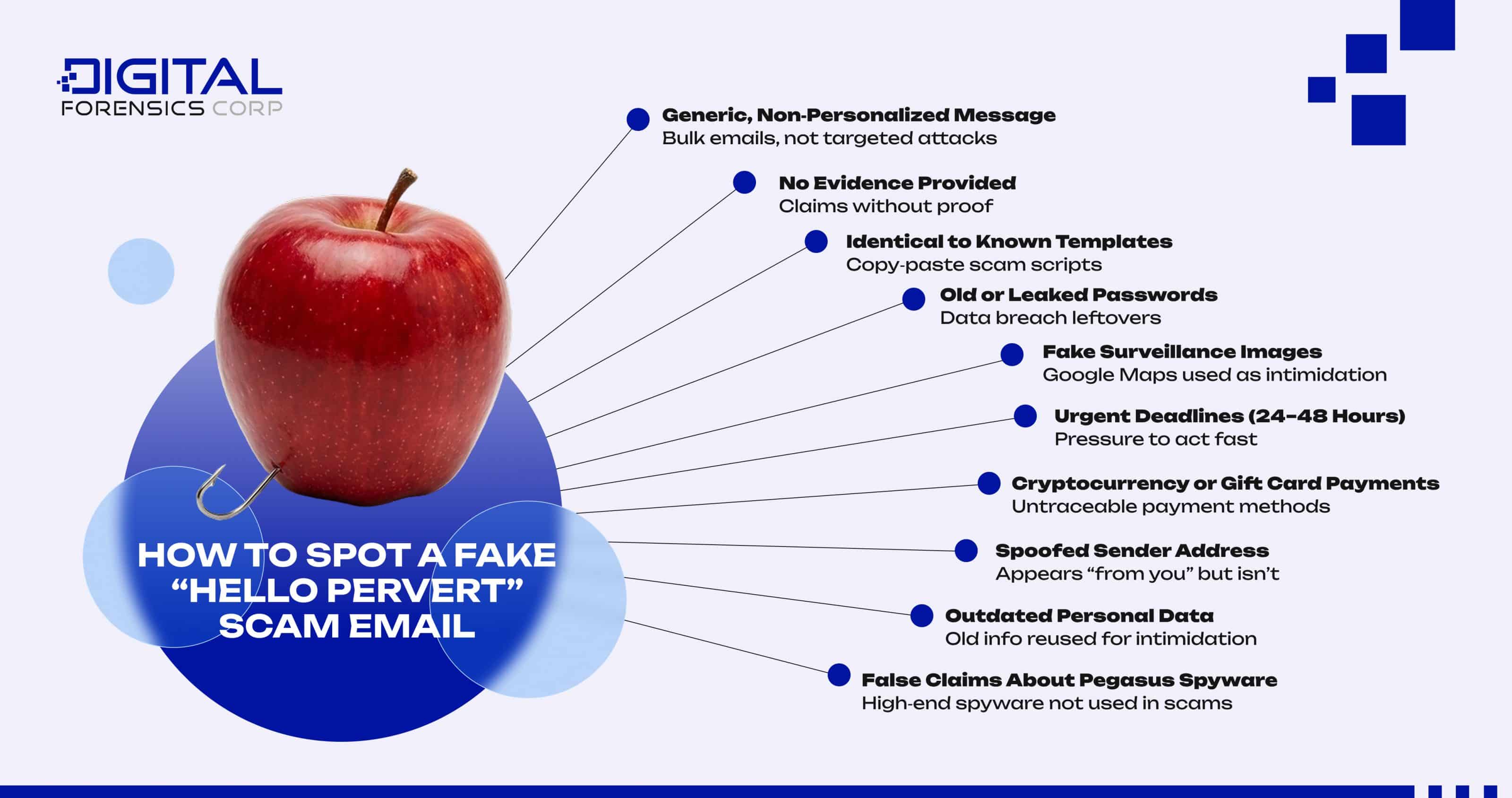
How to Spot a Fake “Hello Pervert” Scam Email
Many “Hello Pervert” sextortion emails are fabricated, and there are consistent warning signs that reveal their true nature.
The following are a few signs of a fake “Hello Pervert” scam email:
- The email is generic and lacks personalization. If the email never mentions your name and uses vague language, it was probably a batch sent out to hundreds of users.
- The email lacks evidence. Sextortionists often lie about incriminating content because it’s a simple way to gain money. However, a real blackmailer would typically include proof to increase pressure, while scammers rely solely on claims and pressure tactics.
- The wording and structure are identical to known scam templates, which can often be found on forums or social media platforms. ‘Hello Pervert’ emails, for example, are easy to find on Reddit.
- The claims don’t match your reality. The scammer will make many claims of your activities and possessing video footage of you. However, these claims are one size fits all and may not be relevant to you.
- The email includes an old or previously used password, typically sourced from a past data breach. Blackmailers often target emails uncovered in a previous data breach, hoping you’ll panic and believe you’ve been hacked and blackmailed even when the threat is completely fabricated.
- The message includes images of your home. Using images from Google Maps to create a false sense of surveillance is a documented tactic.
- The email creates urgency with short deadlines, often 24 to 48 hours, to pressure quick decisions under the threat of imminent exposure.
- Payment is requested through cryptocurrency or other methods of payment that are difficult to trace, such as gift cards.
- The email appears to come from your own account, often due to email spoofing rather than actual hacking.
You may also notice that the message contains outdated passwords or references to personal data. This information is often sourced from old data breaches and reused to make the threat appear legitimate.
Many “Hello Pervert” emails also reference advanced spyware such as Pegasus. However, this type of software is typically reserved for high-profile surveillance operations and is not used in mass email scams.
The Myth of the Pegasus Spyware Threat
A common variation of the “Hello Pervert” scam includes claims that your device was compromised using Pegasus spyware. The message may state that this tool was used to access your camera, monitor your activity, and record private moments.
In reality, this claim is highly misleading. Pegasus is an advanced and extremely expensive surveillance tool developed for use by government agencies. It is typically deployed in targeted investigations involving high-profile individuals such as journalists, political figures, and suspected criminals. Its use requires significant resources, legal authorization in many cases, and sophisticated infrastructure.
It is not a tool that cybercriminals use in mass email scams. The “Hello Pervert” spam email is distributed to thousands of random email addresses at once. The scale and lack of targeting directly contradict how Pegasus is actually used. There is no financial or operational logic for a scammer to deploy such a high-cost tool in a low-value phishing campaign.
In short, if an email claims Pegasus was used against you in a sextortion scenario, it is almost certainly a bluff.
When a ‘Hello Pervert’ Sextortion Email Becomes a Real Threat
Although some cases are fake, real sextortion does exist. A legitimate threat typically includes verifiable evidence, such as screenshots or files, and may reference specific individuals or platforms.
In these cases, the risk shifts from psychological manipulation to actual exposure. The attacker may have obtained content through compromised accounts, malware, or previous interactions.
Malware Risks in ‘Hello Pervert’ Sextortion Emails
Some sextortion emails are designed not just to scare you, but to infect your device. These messages may include links or attachments that claim to contain incriminating footage.
Clicking on these links can result in malware installation, allowing attackers to access your files, monitor activity, or steal login credentials. This transforms a fake threat into a genuine security breach.
For this reason, you should never interact with attachments or links in suspicious emails, regardless of how convincing the message appears.
Should I Ignore ‘Hello Pervert’ Sextortion Emails?
‘Hello Pervert’ emails are hoaxes the majority of the time. However, you should still proceed with caution when deciding how to respond. You need to verify the threats and make sure that they are not real.
Take note of the warning signs that we previously mentioned, but there will be many red flags that the email is a scam. If the email threats are fake, it’s best to ignore them. Responding to the blackmailer will only confirm the email address is active, making you a target for more scams.
Steps To Take If You’re Targeted by a ‘Hello Pervert’ Sextortion Email
Receiving a sextortion email is scary. However, it’s important to keep a cool head. Acting in a panic can cause you to make a vital error. Instead, stay calm and follow the recommended steps to protect yourself. Here is what you should do if you receive a blackmail email.
- Stay calm and avoid making impulsive decisions. The scammer is relying on you to act out of fear and make irrational decisions. We understand that these threats are intense, but take a deep breath and collect your thoughts before you proceed.
- Don’t pay the blackmailer. You should never comply with a blackmailer’s demands. Paying the criminal often results in more demands and threats. It also communicates that you are susceptible to their tactics.
- Save the email. Victims should preserve sextortion emails and document them. Include email header data and attachments. If you delete the email, you erase critical data that can be used by cybercrime experts in an investigation.
- Avoid clicking any links or downloading attachments. While you should document these as evidence, it’s important not to open them. Doing so can deploy malware on your device, which can give the scammer legitimate access to your data.
- Report the email to your service provider. Email platforms can suspend or terminate an account if enough users report the sender. They can also flag the sender as spam. This reduces the chances of others falling victim to the same scammer.
- Secure your account. Change your password and ensure that it has the characteristics of a strong password. You should also enable two-factor authentication (2FA) and take additional measures like scanning your device for malware.
- Notify law enforcement. Your local police can help you verify the validity of the email and file an official report that documents the event. They may also conduct an investigation to locate and unmask the perpetrator responsible.
- Notify your workplace IT team if the email was sent to a work account. This is important, as you may not be the only employee that has been targeted in the attack. Furthermore, the exposure of your work email may suggest a company security issue.
- Check if your credentials were exposed in a data breach. It is common for “Hello Pervert” scammers to target email addresses that were previously leaked. Use services like Have I Been Pwned to see if your email and other data have been exposed.
These steps allow you to protect your data, reduce risk, and contribute to broader efforts to combat cybercrime.
How to Prevent Sextortion and ‘Hello Pervert’ Email Harassment
Preventing ‘Hello Pervert’ sextortion emails requires a proactive approach to cybersecurity. Strong digital habits significantly reduce your exposure to these threats. Using unique and complex passwords across all accounts is essential. Enabling two-factor authentication adds another layer of protection, making unauthorized access more difficult.
Keeping antivirus software updated and running regular scans helps detect potential threats before they cause harm. Spam filters also play a critical role in blocking malicious emails before they reach your inbox.
‘Hello Pervert’ Emails: When to Seek Professional or Legal Support
Taking early action improves the chances of resolving the situation before it escalates further, but some situations require more than basic precautions. If the threat involves real content, ongoing harassment, or potential exposure, professional assistance may be necessary.
Cybersecurity experts can analyze threats, trace attackers, and preserve digital evidence. Law enforcement agencies can document the crime and initiate investigations, especially in cases involving financial extortion or privacy violations. Cybersecurity professionals can help by providing integral data that supports identification efforts.
The “Hello Pervert” email scam is effective because it exploits fear, not because it reflects reality. Most threats are empty, but they are designed to feel personal and urgent. Understanding how these scams operate allows you to respond with confidence rather than panic. The more informed you are, the less power these attackers have.
Digital Forensics Corp. can help you secure your account, document evidence, and organize your case using advanced digital forensics. Our team works with complete confidentiality to protect your privacy while helping you take control of the situation. If you’ve received a “Hello Pervert” email, contact us today for a free consultation with one of our specialists.
For more information on how to handle a sextortion threat, check out our article on what to do when you receive a blackmail email.
FAQ
Document the message, avoid responding, report it to your provider, contact law enforcement, and secure your account and devices. Consider the benefits of working with cybersecurity professionals as you approach your response.
Do not pay. Report the wallet address and the incident immediately.
Look for proof. If none is provided, the claim is likely false. While doing so, it’s important to remember not to click any links or open any attachments.
No, but most are. Real cases usually include evidence. That said, you need to treat all threats seriously and take the necessary precautions to protect yourself.
Report, block, and strengthen your account security. Additionally, you should avoid oversharing and regularly audit your digital footprint to determine if your personal data is available online.