Trying to remove nudes from the internet? Learn how to find leaked images, request removals, and protect your privacy with expert guidance.
We are living in a world of constant online presence. Whether for personal connection or professional networking, maintaining a digital footprint is almost unavoidable. But the more we share, the more vulnerable our most private moments become to those who seek to exploit them. This lays the groundwork for one of the most devastating forms of digital abuse: the non-consensual sharing of intimate imagery.
Whether the content was released by a cybercriminal or an ex-partner, discovering that your nudes have been shared online without your consent is emotionally distressing. It is a crime that turns a person’s vulnerability into a tool for harassment or extortion, often leaving victims feeling a sense of intimidation, panic, and shame. However, you must understand that none of this is your fault. Predators and extortionists train themselves to play into human psychology, leveraging your fear of reputational damage to force compliance.
Timely action is the only way to neutralize the power these perpetrators hold over you. By taking control of the narrative, capturing forensic evidence, reporting the crime to platforms, and speaking with an expert investigator, you can reclaim your digital identity. Continue reading to learn more about how to remove nudes from the internet, how to identify where your images may be circulating, and what steps you can take to protect your future.
How to Find Out If Your Nudes Are Online
Discovering the extent of a leak is often the most emotionally taxing part of the recovery process. However, knowing exactly where the content lives is the only way to begin a targeted removal campaign. If you are wondering how to find out if your nudes are online, start by using a reverse image search tool.
Services like Google Lens or specialized search engines can help you track where an image has been indexed. These tools don’t just find identical photos; they find visually similar content, which is crucial if a perpetrator has slightly cropped or filtered the original file to evade detection.
You should also perform manual searches using “dorking” techniques, combining your name or social media handles with specific keywords related to adult forums or image-hosting sites. It is vital to approach this with extreme emotional care. The goal is to identify which URLs need to be removed, not to subject yourself to the toxic comment sections that often accompany these leaks.
If you notice a sudden influx of friend requests from strangers or unusual comments on your public profiles, these are often signs that content is circulating in private groups or message boards. In many cases, perpetrators will use “teaser” content to lead users to a secondary, hidden link where the intimate media is hosted. Identifying these bridge links is a key step in a professional investigation.
Can You Get Your Nudes Off the Internet?
We must set realistic expectations: the internet never truly forgets, but it can be made to stop showing. There is a technical difference between removal (deleting the file from a server), de-indexing (removing the link from search results), and suppression (pushing the negative content so far down that no one sees it).
While you might not be able to wipe every single byte from a rogue server in a non-compliant jurisdiction, you can achieve meaningful control. By removing the content from Google, Bing, and major social media platforms, you effectively cut off a large portion of the traffic to those images. Complete erasure is a long-term battle, but making the content invisible to the general public is an achievable and powerful victory.
What to Do Before Requesting Removal of Nudes
Before you send a single email to a site administrator, you must gather your evidence. Scammers and spiteful ex-partners often delete and re-upload content once they realize you are fighting back. They may also try to deceive the authorities by claiming the content was shared with permission. Having a forensic record ensures that law enforcement and platforms take your claim seriously. This documentation is your chain of custody, proving exactly what was posted, by whom, and when.
The Victim’s Evidence Protocol:
- Capture full-page screenshots. These must include the browser address bar (URL) and the system clock on your computer.
- Document the source. If the images were sent via a specific app (Snapchat, WhatsApp, Instagram), screenshot the profile of the sender.
- Save direct image URLs. Right-click the image and select “Copy Image Address.” This is the direct link to the server file, which is often different from the page URL.
- Log extortion attempts. If the leak is accompanied by a demand for money, save every message, voice note, and payment request.
- Identify time stamp data. Note when you first discovered the leak versus when the post was originally uploaded.
- Maintain integrity. Do not edit, crop, or blur the screenshots. Altered evidence is often inadmissible in court or ignored by platform moderators.
- Store evidence securely. Store this evidence in a secure, encrypted folder or password-protected cloud drive that only you can access.
Steps for Victims of NCII to Remove Their Nudes from Sites
The steps you will need to take depend largely on where the content was published. Popular search engines like Google and Bing are actively combatting non-consensual intimate image abuse. Among other initiatives, they offer a reporting tool to remove links to such content from their search results.
Reporting NCII Content on Google
Google has a removal request form where you or an authorized representative can submit a request to remove links to intimate content that were created or shared without consent. For Google to consider content removal, the content must meet 3 requirements:
- The imagery must show you — or the individual you’re representing — partially or fully nude, in a sexual act, or an intimate state.
- You or the individual you’re representing either didn’t consent to the public release of the explicit content or didn’t consent to the imagery or act, and it was shared publicly.
- You must not currently be getting paid for this content.
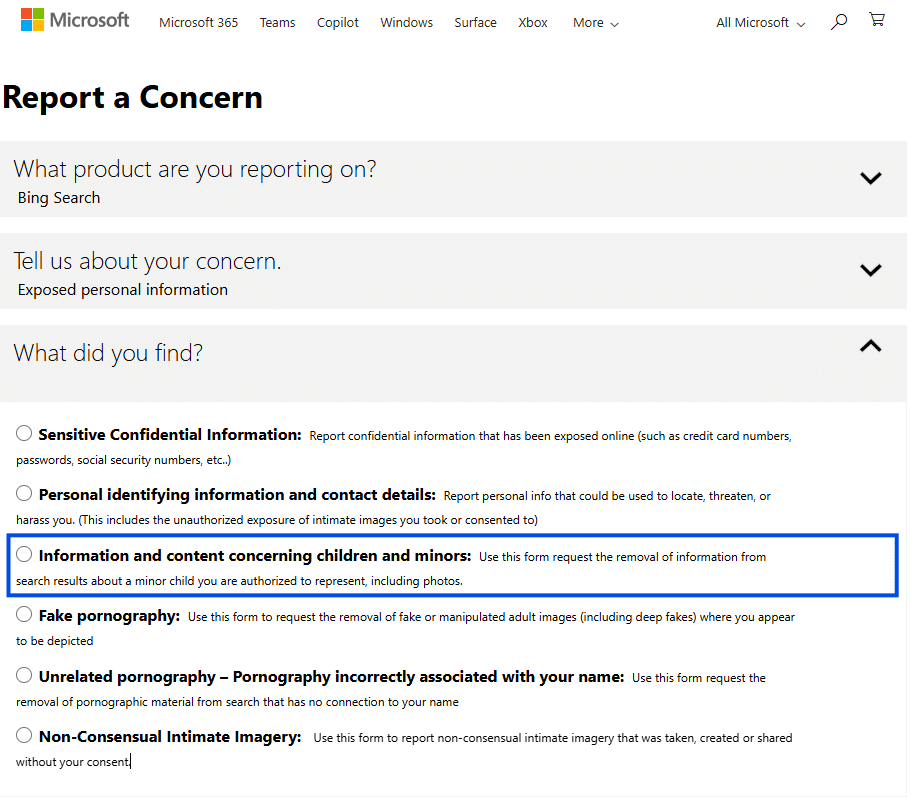
Reporting NCII Content on Bing
Microsoft has recognized the devastating impact of intimate image abuse since 2015 and, over time, has taken steps to protect victims of the crime on their platforms. Microsoft’s Bing was the first search engine to partner with StopNCII.org, a tool to prevent and report Sextortion or image-based sexual abuse, in 2024. The company also has a centralized reporting portal for victims to report content or conduct that violates Microsoft’s policies regarding intimate content shared without consent. There are three steps to reporting non-consensual intimate imagery on Microsoft.
- Visit “Report a Concern” to start the form.
- You will need the URL for the webpage where the content is found and the URL for the content itself if there is one.
- Check for email confirmation that you submitted a report.
Reporting for NCII abuse on Microsoft is for users over 18 years old. Minors should select the child sexual abuse material (CSAM) option instead:
If Published on a Social App…
If Published on an Adult Website or Message Board
Adult websites often operate under different legal standards than standard social media platforms, but many of the larger mainstream hubs comply with the Digital Millennium Copyright Act (DMCA) to avoid legal liability. Navigating these sites can be distressing, but you must remain objective.
Locate the “DMCA,” “Legal,” or “Contact” link, which is usually found in the footer of the website. Your request should be clinical, firm, and devoid of emotional pleading. Simply state that the content was posted without your consent, you are the subject of the imagery, and it violates their Terms of Service and NCII policies.
If the content is on a niche message board or a “revenge porn” site that intentionally ignores takedown notices, do not engage with the users or the administrator in the comments. These sites thrive on the “Streisand Effect.” The more engagement a thread receives, the higher it climbs in search engine rankings. By arguing with trolls or pleading with the uploader, you are inadvertently signaling to algorithms that the page is relevant, which keeps it visible.
In such difficult cases, the strategy shifts from direct deletion to total isolation. Focus your energy on the search engines and third-party removal services that can build a wall around the site, effectively burying it where no one can find it without a direct link.
What is a DMCA Takedown Notice?
The Digital Millennium Copyright Act is a copyright law passed in 1998 that provides creators with protection when their content is used without permission. When it comes to the non-consensual sharing of intimate images, the DMCA may actually grant the owner of the content copyright protections. If the victim is the owner of the content, they can use a DMCA Takedown Notice to remove images or videos from certain websites.
Unfortunately, DMCA Takedown Notices are not a completely reliable solution to image-based sexual abuse. The notice will only apply for the specific instance of your content being published, meaning it can be reuploaded. It’s best to consult with a legal professional when considering DMCA Takedown Notices and to explore your legal options.
Other Resources for Victims of NCII
There are several resources that can help victims remove private online content related to intimate imagery, including those targeted in nude blackmail cases, many of which are run by organizations specifically created to combat image‑based sexual abuse. While these services offer valuable support, it’s important to get clarity on their process of detection and removal of NCII content.
- Stopncii.org: This free tool is designed to remove and prevent the upload of non-consensual intimate content across platforms. Using hash-generating technology, the tool creates a unique hash value for images or videos submitted by victims. Participating companies will search for matching hashes and prevent the content from being uploaded to their platforms. This hash is then shared with participating platforms like Meta, TikTok, and Bumble. These platforms add the hash to their “blocklist,” which automatically prevents the images from being uploaded to their servers in the future. This proactive shield works without the platform employees ever seeing your private photos, preserving your dignity while ensuring the images cannot go viral on major networks. Combining these non-profit resources with professional forensic investigations creates a comprehensive safety net that covers both current leaks and future threats.
- NCMEC: The National Center for Missing and Exploited Children is a well-established organization that fights CSAM. They run the Take It Down tool, which is similar to StopNCII.org but exclusively for minor victims, and the CyberTipline, a centralized portal for reporting the online exploitation of children. The NCMEC works in partnership with the FBI and can track national trends through their reporting portal.
- Cyber Civil Rights Initiative: The CCRI offers support for victims in referrals to pro bono lawyers, a 24/7 hotline, and educational materials. The nonprofit is also active in legal advocacy for victims of NCII abuse, pushing for stronger laws against the crime.
- Law Enforcement: Reporting the crime to local authorities is an important step in addressing and taking down non-consensual intimate content. The local police can assist in filing a report to officially document the crime, launch an investigation to identify the culprit, and help guide you on the next steps you should take.
- Private Security Firms: Using digital forensics, cybersecurity firms can trace the online footprint of image-based abuse back to its original source. They have experts that monitor the internet and remove any non-consensual publishing of your intimate content. Digital Forensic Corp., for example, has a team of professionals who work tirelessly to protect the privacy of their clients and can even investigate NCII abuse to discover the identity of the perpetrator responsible. Contact us today for a free consultation with one of our specialists.
How to Protect Yourself After Removing Nudes
Once the immediate crisis has subsided and the majority of links have been neutralized, you should pivot to a defense-in-depth strategy. This isn’t about blaming yourself for what happened; it is about ensuring that a predator can never gain a foothold in your digital life again. Tighten your privacy settings on every social media account, moving from “Public” to “Friends Only,” and audit your follower lists for accounts you don’t personally recognize.
You should also implement the following security measures to harden your digital perimeter:
- Two-factor authentication (2FA). Use app-based authenticators rather than SMS to protect your cloud storage and email.
- Regular digital footprint audits. Set up “Google Alerts” for your name and common aliases to receive an email the moment a new link is indexed.
- Password hygiene. Use a dedicated password manager to ensure that a breach on one site doesn’t give a hacker access to your entire life.
- Reputation management. Actively cultivate a professional online presence. By building a strong LinkedIn profile or a personal portfolio site, you can claim the top search results for your name.
This proactive approach ensures that a single malicious act by another person does not define your digital future. By burying the past under a mountain of positive, professional data, you reclaim your narrative and your peace of mind.
What If You Can’t Delete the Images Completely? When to Get Professional Help
There are instances where a standard takedown request is not enough. If you are dealing with a persistent harasser who re-posts content every time it is taken down, or if the images have spread across dozens of unmoderated forums, the DIY approach can become a full-time job that leads to severe burnout.
When to Get Professional Help Removing Nudes from the Internet
Expert help is appropriate when you feel the situation is escalating beyond your tactical control. Professional digital forensics and reputation management teams do not just send emails; they use automated crawler tools to monitor the web 24/7 for new uploads of your specific digital signature. These teams can perform bulk removals and work directly with legal departments to identify anonymous posters through IP tracing and metadata analysis.
If you find that you are spending hours every day checking for your images, or if the leak is part of a larger blackmail or sextortion scheme, seeking a specialist provides a necessary emotional buffer. Deleting nudes from a massive leak requires technical tools that most individuals simply do not possess. Professionals can also assist in search engine suppression, creating a flood of positive, neutral content that pushes any lingering negative links to the second or third page of search results, where they are statistically unlikely to ever be clicked.
FAQ – Removing Nudes from the Internet
Yes, in the vast majority of jurisdictions, this is classified as “Non-Consensual Intimate Imagery” (NCII) or revenge porn. It carries both criminal and civil penalties.
If the person in the photo is a minor, it is a severe federal crime involving child sexual abuse material (CSAM). For adults, it is a crime in nearly all U.S. states and many countries globally.
Yes. Many people have been sentenced to prison for revenge porn and sextortion. Law enforcement takes these cases much more seriously now than in previous years.
It is legal for two consenting adults to share images privately. However, that consent does not extend to sharing those images with third parties or the public.
Absolutely. Victims can sue for intentional infliction of emotional distress, invasion of privacy, and copyright infringement. Civil lawsuits can result in significant financial judgments against the harasser.
It does not matter. The law focuses on the distribution of the images. Sending a photo to one person does not grant that person a license to publish it to the world.
Document everything. Take screenshots of the post and the URL, then report it to the platform using their NCII tools. Do not delete your copies of the evidence.
Dr. Viktor Sobiecki
Currently serves as the Chief Technology Officer (CTO) at Digital Forensics Corporation, where responsibilities span the leadership of advanced cybersecurity initiatives, data breach incident responses, and corporate strategic planning.